SIEM Integration & User Access
What You'll Learn
- How to Integrate Logichub SIEM?
- How to access [Kibana] (https://help.logichub.com/docs/siem-integration#kibana-user-access---logichub) through the Logichub instance?
SIEM Integration: Security Information & Event Management
SIEM offers the opportunity to integrate with different security products. It streamlines administration so you can correlate vulnerabilities and logs from systems and network traffic to detect security threats. LogicHub security can be integrated with SIEM systems through an API and thus collect information on vulnerabilities. LogicHub also builds specific integrations for different SIEM systems. Contact us, and we will tell you more about integrations with your SIEM system.
Logichub flexible configuration enables you to:
All our modules include a powerful feature that injects informational headers for each request.
LogicHub Support🛠
Logichub Data Engineering Team support and help you out in case of any issue.
Our SIEM provides the facility to collect/integrate from a variety of data sources
-
Filebeat/Beats services configuration will enable users to set up which data to be sent and what kind of data (SSH Logs, Audit Logs) through the server. LogicHub provides the URL and port for which the user needs to configure the server and send the data to the URL.
-
Logichub will help you configure at your end to pull the Amazon Simple Storage Service (Amazon S3) data which generally manages Amazon Simple Queue Service (Amazon SQS) messages into LogicHub SIEM.
-
LogicHub will provide the Token / URL. Users will use the token and the URL to send the data to LogicHub via HTTP calls (both encrypted/raw).
-
User can also send logs to our SIEM can integrate seamlessly any Linux logs/streaming logs via standardized via open-source file-beat / elastic beats
-
LogicHub SIEM can collect data with minimal hassle from your Office management system/ Windows
-
Define one or more target Syslog servers, and LogicHub provides the URL and port for which the user needs to configure the server and send the data to the URL.
-
Filter the events that are sent to all the configured Syslog servers over encrypted or non-encrypted protocols.
The configuration is built as a list of values. Each set of parameter values must be specified in correlation with the other parameter values in the configuration. This allows the system to determine the settings for each target server.
Supported protocols
Can use any of the following protocols to send messages:
| Type | Protocol |
|---|---|
| Encrypted protocols | TLS |
| Non-encrypted protocols | TCP UDP |
Syslog messages can be sent to multiple Syslog servers in different ways:
- User can send Syslog event/stream to us via different kinds of Syslog servers like rsyslog, Syslog-NG etc.
Additional Information
Currently, LogicHub support both RFC-5424 and RFC-3164 Syslog format.
-
A single message can be sent to multiple servers by configuring a single XSLT file.
-
Multiple messages can be sent to different Syslog servers, and formatted differently for each server, by configuring multiple XSLT files, formats, and code-message lists. The code-message lists must match, meaning they must contain the same number of items in the same order.
SIEM/SOC tools provide the possibility to include these headers.
Below is an example of the most famous SIEM/SOC tools.
# you need to add logichub headers in Elasticsearch output configuration: https://www.elastic.co/guide/en/beats/filebeat/current/elasticsearch-output.html#_literal_headers_literal
module: nameOfModule
access:
enabled: true
var.paths: ["/path/to/log/access.log"]
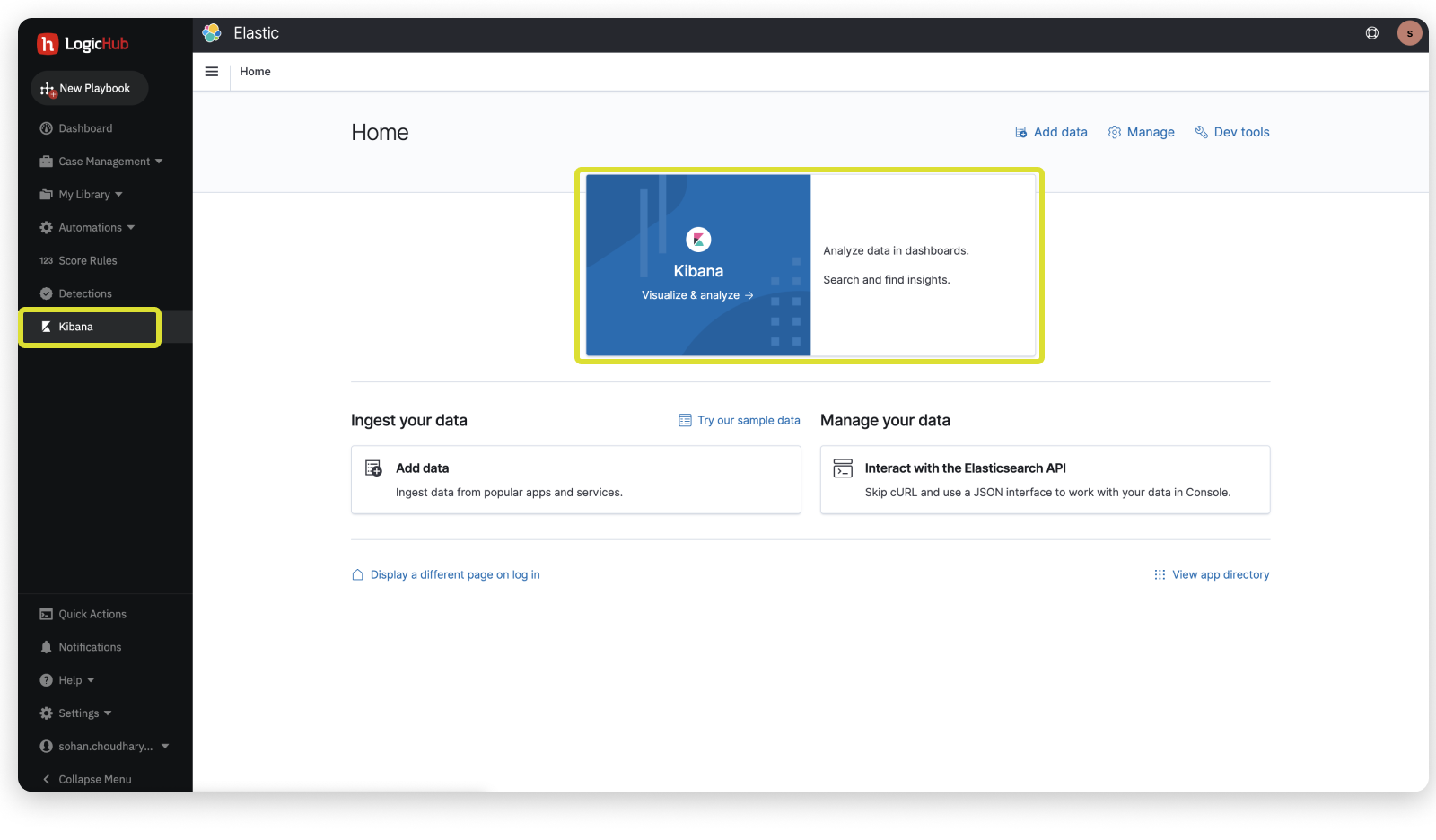
Kibana User Access - LogicHub
LogicHub provides the following permission (Groups Permission), to further understand refer User Management.
SIEM client Kibana access
All the users avail of the Logichub SIEM services will have access to the Kibana through the Logichub instance by default.
LogicHub Support🛠
Contact us for further assistance and/or to acquire Kibana access on the Logichub platform.
Updated almost 2 years ago